How can cyber-physical systems and critical infrastructure be secured against evolving cyber threats and disruptions? CyberUnite addresses this challenge by bringing together interdisciplinary expertise across artificial intelligence, systems security, and networked infrastructure to develop advanced cybersecurity solutions. Our research focuses on explainable threat detection, Zero Trust enforcement, secure system foundations, and cyber-digital twin environments, enabling real-time insights, resilient system operation, and proactive defence against sophisticated attacks. Through this integrated approach, CyberUnite aims to strengthen the security, reliability, and trustworthiness of the systems that underpin modern society.
Research
Program Areas
Explainable AI Security
Developing intelligent, explainable threat detection systems that provide real-time insights and support transparent, trustworthy decision-making in cyber-physical systems.
Secure System Foundations
Designing core mechanisms for trust, privacy, cryptography, and AI security to establish a robust and reliable foundation for cyber-physical systems.
Zero Trust Enforcement
Applying Zero Trust principles using programmable data planes to ensure secure, continuous verification of all system interactions and prevent unauthorised access.
Cyber-Digital Twins
Creating cyber-digital twin environments to simulate, test, and evaluate system resilience against advanced cyber threats in realistic, controlled settings.
Current Missions
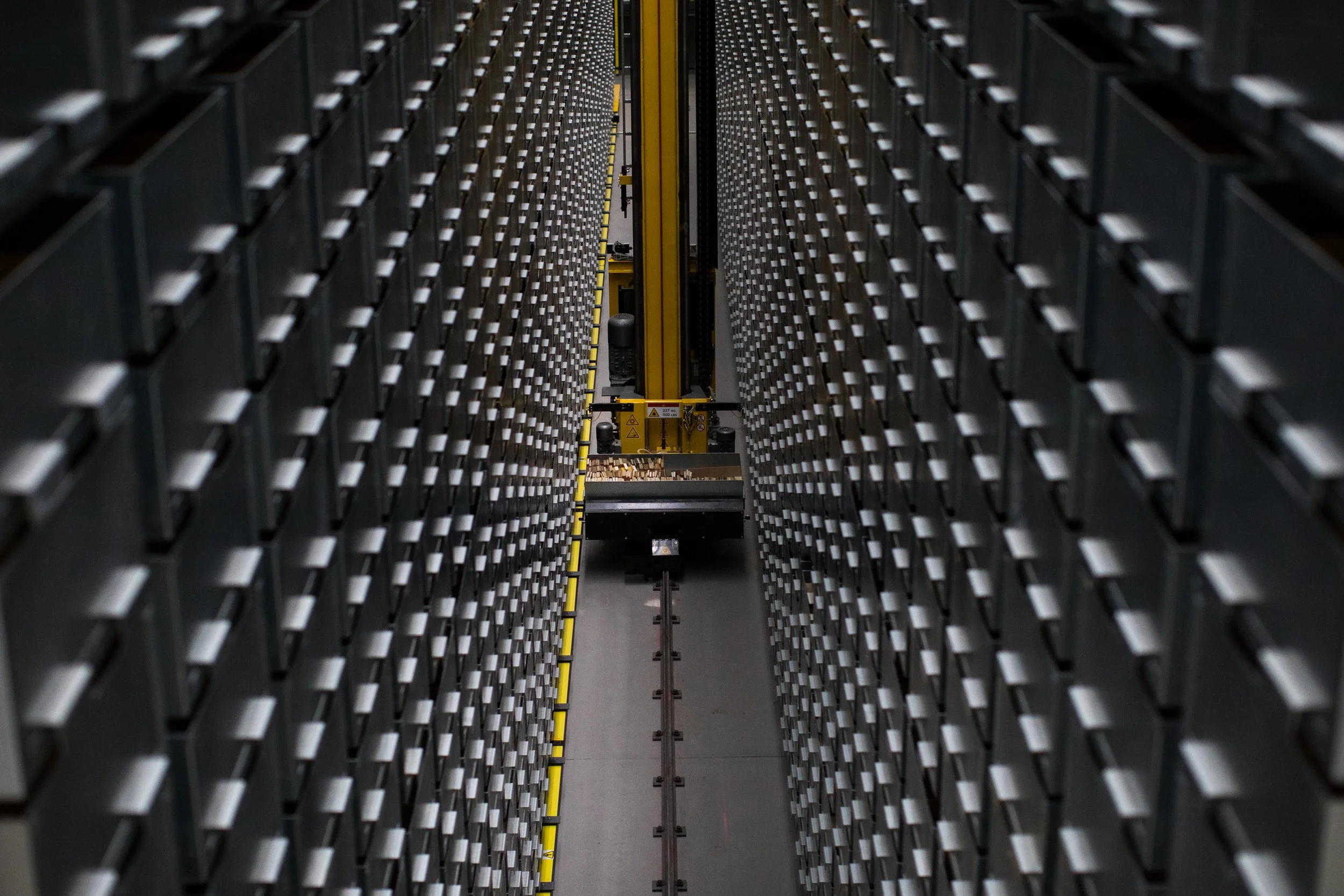
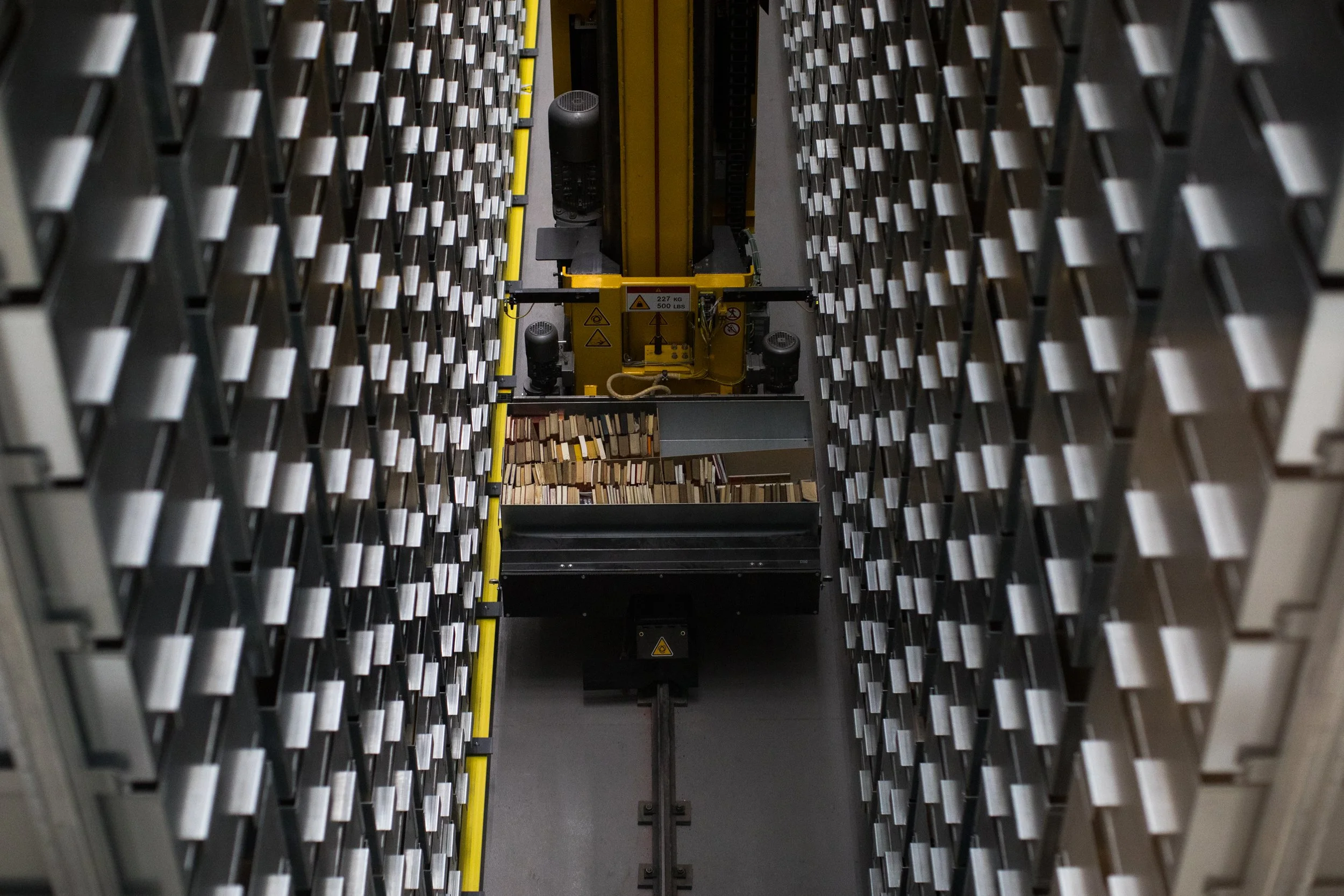
Securing Industrial Systems
Applying CyberUnite technologies to protect real-world cyber-physical systems in manufacturing and industrial environments.
Real-Time Threat Monitoring
Developing platforms that provide continuous visibility into system behaviour and detect anomalies as they occur.
Cyber Range Development
Building realistic simulation environments to test cyber threats and evaluate system resilience in controlled scenarios.
Cross-Border Collaboration
Working with academic and industry partners to develop and validate cybersecurity solutions across diverse infrastructures.